Linux Privilege Escalation and Vulnerability Exploit Script (linPEVES)
linPEVES is a privilege escalation script inspired by linPEAS, a well known linux privilege escaltion vulnerability scanner.
What is Privilege Escalation?
Like any human design, computers have weaknesses which are known as vulnerabilities.
Privilege Escalation (PE) refers to a class of vulnerabilities that allow an unprivileged user to gain privileges that grant them more access or control over a system.
Our Project
Our project identifies and exploits PE vulnerabilities to escalate a user's privileges within a Linux system.
The goal is to allow a user to scan for vulnerabilities within a system and exploit them (or not).
linPEVES Architecture
Background
Created a Linux VM on Amazon Web Services (AWS)
Runs Ubuntu 24.04
Researched and added vulnerabilities to the VM
-
Wrote scripts to exploit them
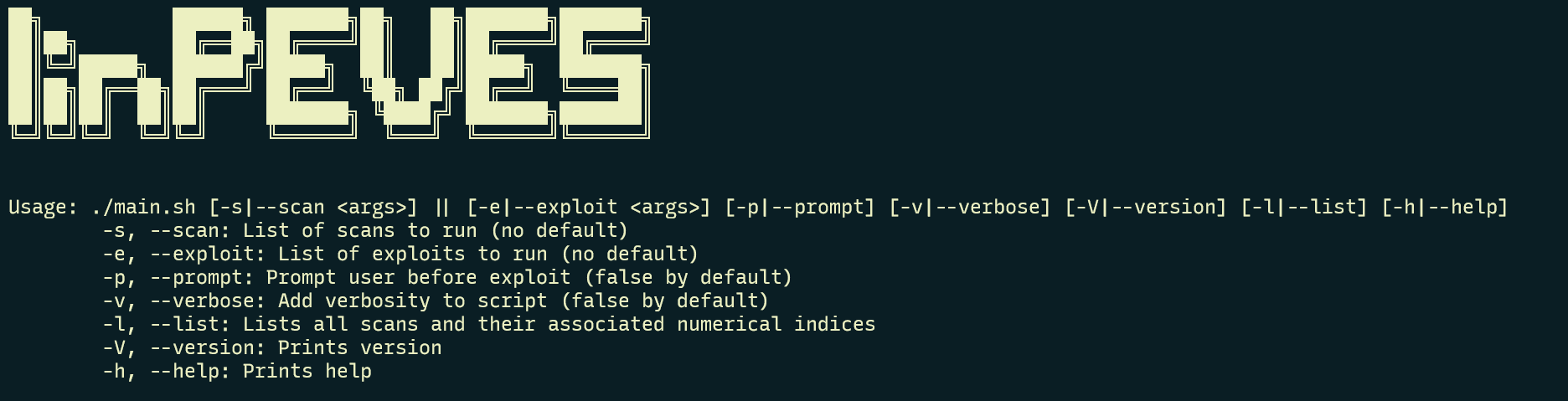
How to Run
Download and Install linPEVES
Change directory to linPEVES/
Decide which scans and exploits you want by running ./main.sh --list. See list to the right:
| # | SCANS | EXPLOITS |
|---|---|---|
| 0 | cron-scan | cron-exploit |
| 1 | env-var-scan | env-var-exploit |
| 2 | path-scan | path-exploit |
| 3 | pkexec-scan | pkexec-exploit |
| 4 | readable-passwd-scan | readable-passwd-exploit |
| 5 | readable-shadow-scan | readable-shadow-exploit |
| 6 | shellshock-scan | shellshock-exploit |
| 7 | sudo-scan | sudo-exploit |
| 8 | sudoers-scan | sudoers-exploit |
| 9 | systemctl-bin-scan | systemctl-bin-exploit |
| 10 | writable-passwd-scan | writable-passwd-exploit |
| 11 | writable-shadow-scan | writable-shadow-exploit |